One of our current research projects called the EFPF (European Connected Factory Platform for Agile Manufacturing), www.efpf.org, is about digital manufacturing ecosystems to be established through a federation of cloud-based manufacturing platforms. Prior to entering the EFPF federation, each of the platforms was designed to provide their own security and privacy controls. Platform federation brings new challenges and technical issues, one of them being federated identity assurance. Hence we look for an effective cybersecurity architecture to connect identities across platforms and enable advanced threat prevention, detection and mitigation.
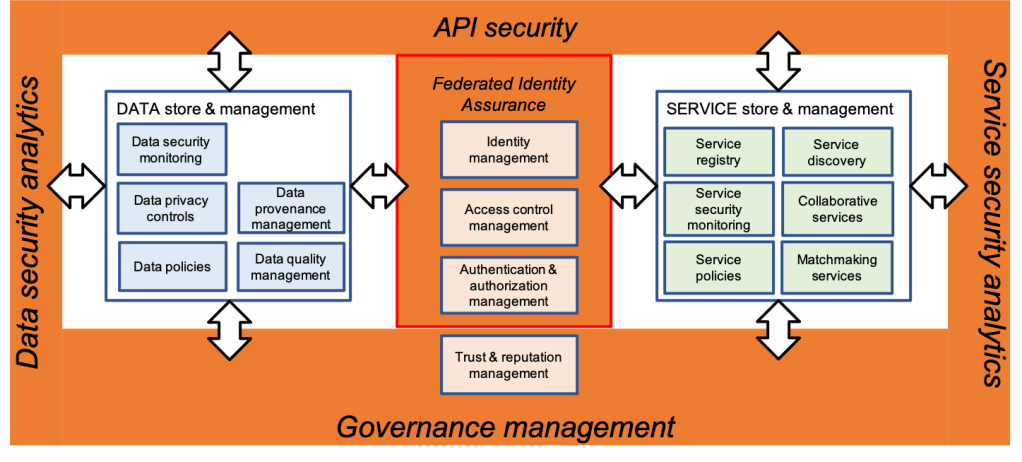
Apart from federated identity assurance, such an architecture needs to address also conventional cloud-based security and privacy controls, authentication and non-repudiation, risk management, policy management, and so on. We also place great emphasis on securing data stores and service stores offered through the platform ecosystem (see Figure 1).
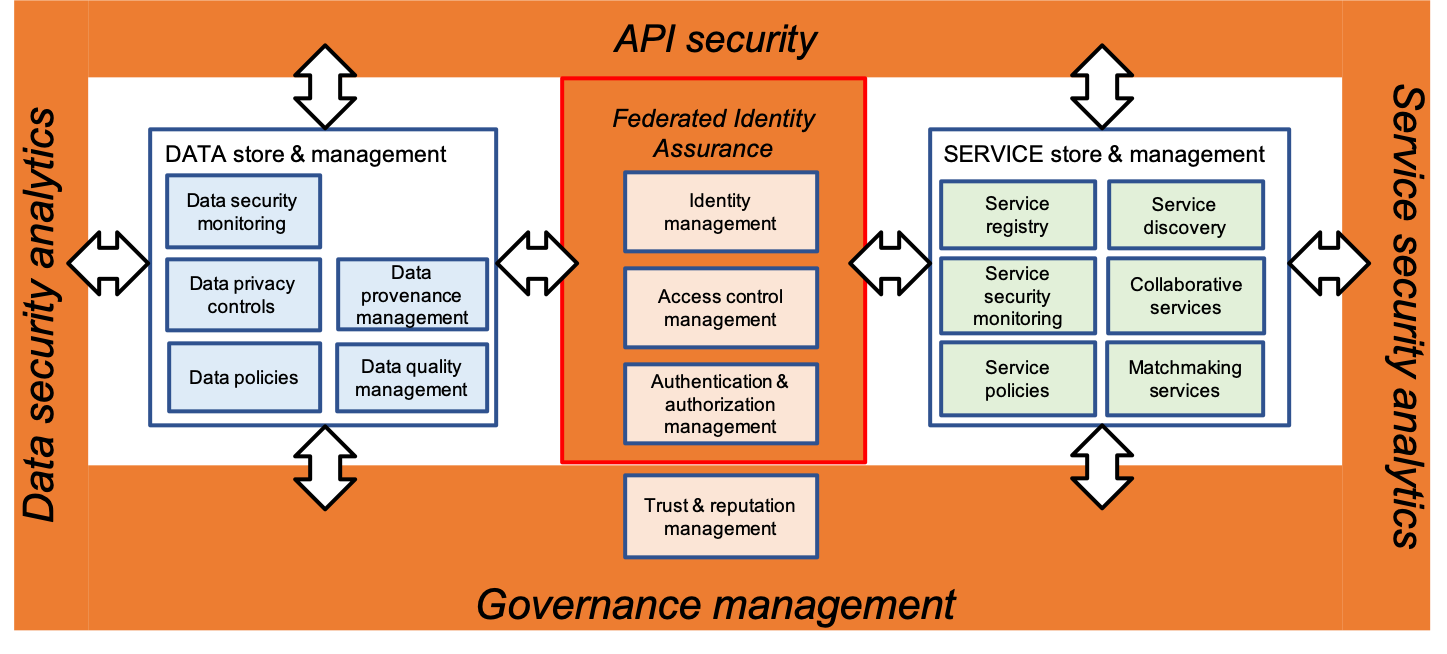
Figure 1 illustrates the major features of a preliminary cybersecurity architecture for a digital platform federation.
- DATA store & management – it calls for continuous security monitoring to ensure data confidentiality, data integrity and availability; data provenance mechanisms to support the lifecycle of provenance information; data quality mechanisms to ensure the trustability and evaluate the quality of data; data centric policies enablement and certification; privacy aware data processing and storage; and more.
- SERVICE store & management – it calls for security service monitoring; secure service registry, service discovery, service orchestration and matchmaking; service centric policies enablement and certification, etc.
Both DATA store & management and SERVICE store & management are in the focus of a cybersecurity middleware that supports:
- API security – to monitor APIs behaviour and raise security alerts
- Federated identity assurance – to provide cloud identity federation and strong authentication
- Data security analytics – for data security monitoring
- Service security analytics – for service security monitoring and threat detection
- Governance mechanisms – for decision making on security practices and responsibilities, risk and resource (asset) management for security, compliance with legislation, regulations, security policies and rules.
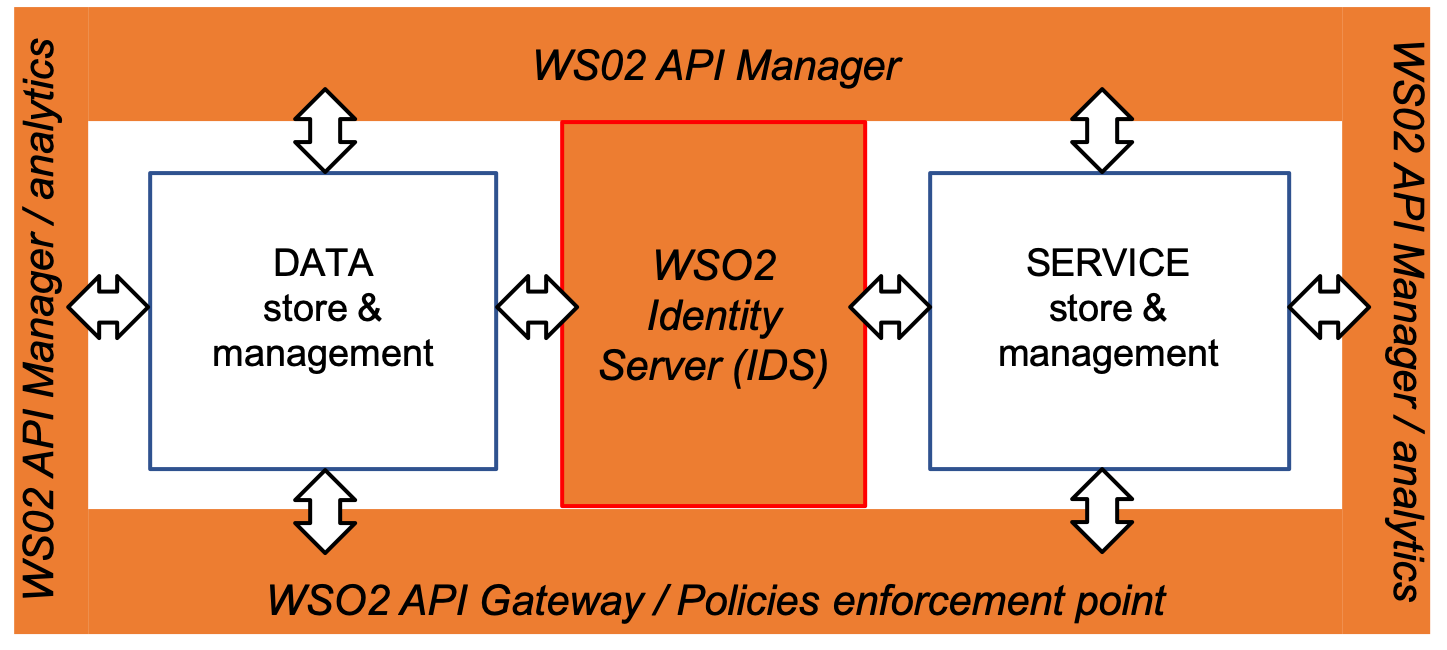
For the implementation, we discovered WSO2 extensible open source technology to be a good candidate to support a wide range of our security requirements. For example, the WSO2 open source Identity and Access Management (IAM) enables strong authentication and federated identity assurance across cloud environments. The architectural features presented in Figure 1 could be plugged into WSO2, as illustrated in Figure 2.
The next step will be to align the above-presented cybersecurity architectural features with the IT architecture of the EFPF platform.


Leave a comment